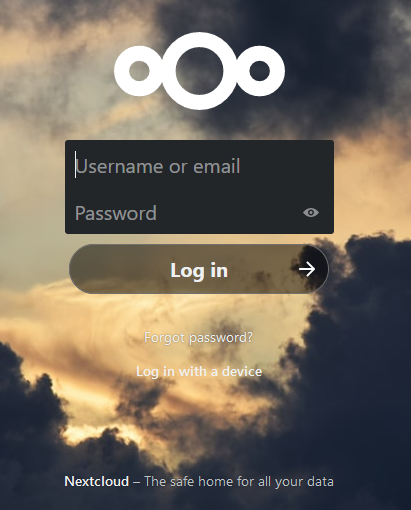
I’ve Installed Nextcloud… Now What?
I’ve been woefully neglecting this blog for FAR too long. Life has been quite busy and honestly, I just haven’t made proper time for it. It’s been so long in fact, I had to archive out of date posts and I’ve not even posted once about Nextcloud. It is a shame on my part because…